We are living in the Digital era where everything is going digital, from making online payments to sharing photos or even running global business, almost every sector today is influenced in some way or the other by digital Interconnectivity. But as our dependency on technology grows, so does the risks that come with it.
This is where Cybersecurity steps in.
Cybersecurity is no longer just an IT concern or something that concerns the major businesses and governments, it also affects individuals, businesses be it small or big, governments and even whole economies. Just like we need to protect our homes from threats like thief etc. we should also be able to protect our digital profiles and assets.
What is Cybersecurity?
Cybersecurity refers to the practice and methodology of protecting data, networks and computers like desktops, laptops, mobile devices, servers from digital attacks, unauthorised access, damage or disruption.
In simple terms, Cybersecurity is about keeping the digital world safe and secure.
Businesses and governments hire cybersecurity experts to protect their valuable stuff like data, networks and hardwares. These protections are designed to defend against cyber threats such as hacking, data theft, malware infections, ransomware attacks, and identity fraud. Cybersecurity applies to anything connected to the internet or a network, from personal smartphones to massive cloud data centres.
Cybersecurity vs Information Security vs IT Security
These terms are often used interchangeably, but they have slight different meanings:
Information Security (InfoSec)
- Focus: The entire “CIA Triad” (Confidentiality, Integrity, Availability) for all information, regardless of format (digital, paper, spoken).
- Scope: Policies, risk management, physical security (locked files), data governance, compliance, and digital security.
- Goal: Protect information assets from any unauthorized access or disclosure.
Cybersecurity
- Focus: Protecting digital systems, networks, programs, and data from cyber threats (hackers, malware, ransomware).
- Scope: A major component within InfoSec, dealing with electronic vulnerabilities.
- Goal: Defend cyberspace and digital assets from attacks.
IT Security (Information Technology Security)
- Focus: Securing the IT infrastructure itself—hardware, software, networks, and physical IT environments.
- Scope: Implementing security controls, managing network access, device security, and often training users.
- Goal: Ensure the availability, integrity, and security of the technology systems that process information
Why Cybersecurity Matters
Cybersecurity failures can have serious consequences on both the digital as well as the real world. In todays world where everything is digital and interconnected, digital security needs to be taken seriously for various reasons:
- Financial Loss: Many cyber attacks are focused either directly or indirectly on Money, online fraud for stealing money from banks are very common, business downtime can lead for huge losses for businesses.
- Information Leak: Data is the new oil. If a business rival gets access to sensitive information/data it can lead to severe consequences or suppose if someone gets access to secret government documents, it can risk entire nations security.
- Reputation Damage: Businesses and organisations run on reputation and brand image that takes years to build but if someone is able to spread misinformation about them it can affect them and same goes for individuals as well.
- Legal and Regulatory Impact: Organisations may get fines imposed on them after security incidents affecting them financially as well as their brand image.
- Individual: Often times attackers target individuals for reasons like money, revenge etc. as many individuals don’t have knowledge on how to protect themselves online so they fall for cyberattacks which can lead to situations which are not only bad for individuals but for their family and business as well.
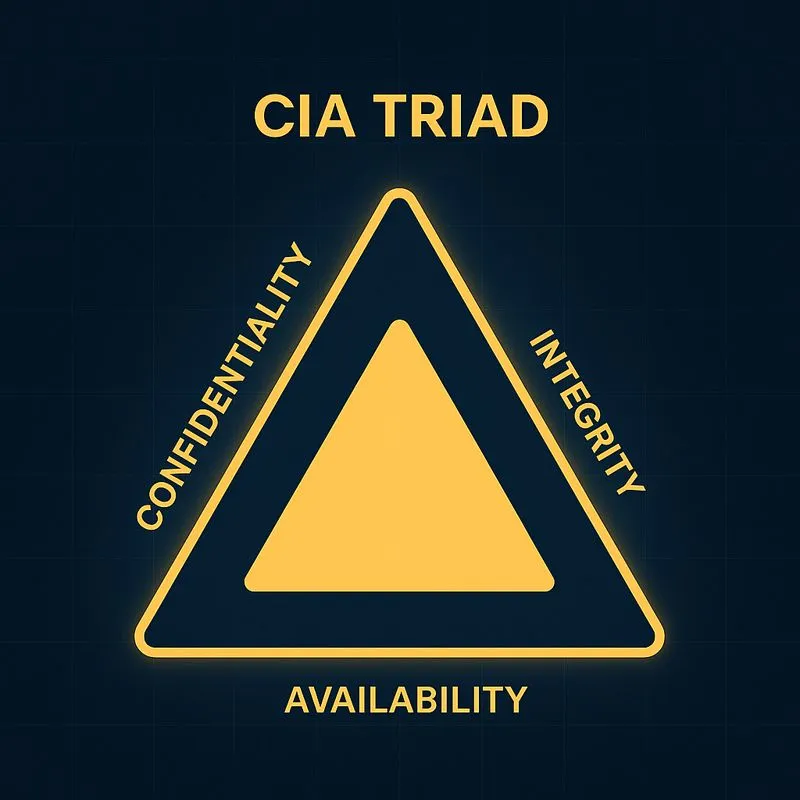
The CIA Triad: The Foundation of Cybersecurity
The CIA triad is a core framework that stands for Confidentiality, Integrity, and Availability. Most cybersecurity strategies are built around these core principles,
- Confidentiality: Ensuring that data can only be accessed by authorised person or system. This principle prevents from unauthorised access of data, it is achieved through measures like encryption, access controls, and user authentication.
- Integrity: It ensures that data remains accurate and complete, it prevents any unauthorised modification or deletion of the data. If the data is somehow tampered during transmission or storage it can lead to serous damage be it government, business or individuals.
- Availability: It ensures that Systems and data are available when required and faces no unnecessary downtime. When a server is down due to any reason and is not able to serve to the requests it is receiving the users tend to move to other similar resources causing damage to the business.
Modern Cyber Threat Landscape
Cyber threats today are more frequent, more automated, and more sophisticated than ever before. As the technologies evolve around us so do the cyberattacks, hackers evolve rapidly using the latest technologies to make sophisticated attacks, most of the times cyberattacks are not like shown in the movies where a hacker breaks into a system with a few clicks, How most common attacks begin:
- Stolen or weak password
- Phishing emails or messages
- Unpatched software vulnerabilities
- Computer misconfigurations
Hackers look for a loophole in digital systems or human errors that can get them access to the System.
Common Types of Cyber Threats and Attacks:
- Malware: Malicious programs/softwares designed to damage or exploit systems, an attacker installs a piece of code into the system that can affect other softwares on the system or the whole system itself, some common type of malware are:
- Viruses and Worms
- Trojans
- Spyware and keyloggers
- Ransomware
- Phishing and Social Engineering Attacks: These attacks exploit human behaviour rather than technical points, in these kind of attack the hacker tries to trick people in revealing sensitive info like passwords, card details, bank account details etc. People often fall for these attacks due to lack of knowledge and training, now organisations have started training their employees for digital awareness. In this attack the attacker often imitates of being someone trustworthy. Common Attack types:
- Phishing Email and messages
- Fake website and login pages
- Credential-Based Attacks: In these attacks the attacker use leaked credentials to gain access to the system, attackers maintain a long list of passwords and other credentials that they can use in an automated way to get into the system, types are:
- Brute force attack
- Credential stuffing using leaked passwords
- MFA fatigue attacks
- Network Attacks: Here the attacker tries to get into the network that the systems are connected to affecting the servers, these attacks can leave the servers and networks unusable, types of attacks:
- DDoS(Distributed Denial of Service)
- Man-in-the-middle attacks
- Web and Application Attacks: These attacks are focused on websites and applications mostly to gain access to the Servers and/or Databases of the website, either to steal any resource or affect the traffic on the website, these attacks include:
- SQL Injection
- Cross-site scripting (XSS)
- API abuse
- Insider Threats: Attackers not only use outside channels but inside channels as well such as human errors, or often times the attacker can be an insider as well with some malicious purpose, related attacks:
- Malicious insiders abusing access
- Accidental mistakes by employees or users
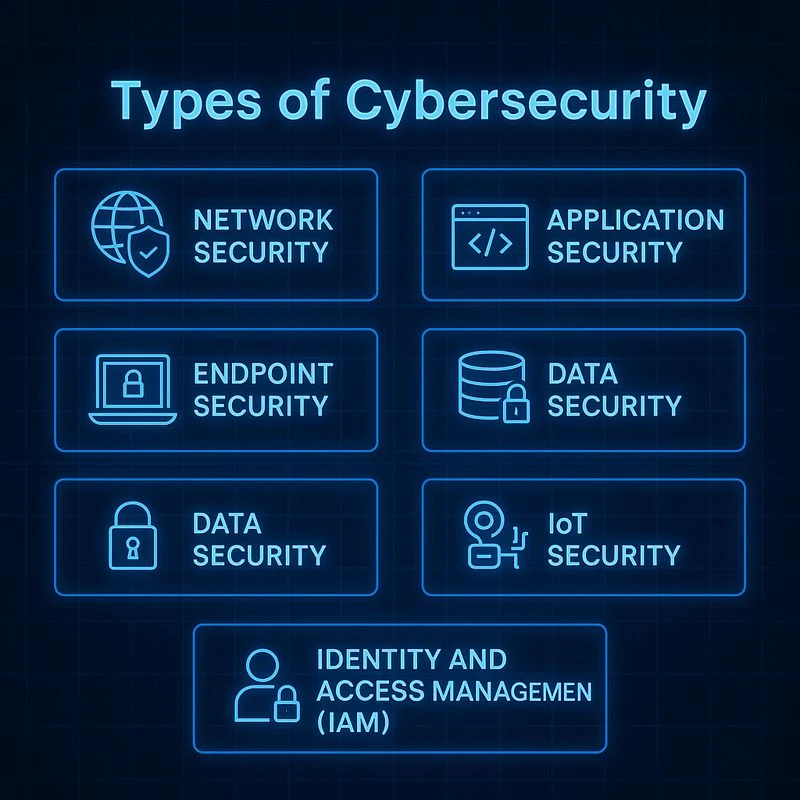
Types of Cybersecurity
There are different measures and types of cybersecurity focusing on different areas in the digital world, lets have a look at them:
- Network Security: It involves the protection of the network that connect the end systems, networks carry the data between any two or more systems, all the communications happen over networks so protecting them is crucial, it is done using tools like firewalls, intrusion detection systems, segmentation, and secure configurations.
- Application Security: Protecting softwares and applications(web and mobile) through implementing secure coding, testing and vulnerability detection, during the SDLC(Software Development Life Cycle) the application is coded in such a way that it is secure for most vulnerabilities and tested heavily to detect any issues and errors.
- Cloud Security: It involves protecting data in cloud environment, technologies and policies are used to protect the data stored in cloud like access control, encryption, monitoring etc.
- Endpoint Security: It means protecting devices like laptops, desktops, mobile phones etc. these devices are connected to a network so they need protection from viruses, malware etc., it is done using antivirus softwares, firewalls, encryptions etc.
- Data Security: Protecting the data from unauthorised access and tampering using methods and tools like data encryption, access control, data loss prevention techniques etc.
- IoT Security: It involves securing devices such as smart home devices, industrial devices, sensors these devices are connected to a network hence protecting them from any unauthorised access becomes necessary.
- Identity and Access Management (IAM): It controls who can access what resources, in other terms allowing the right users (Person or Machine) to access the right resources.
Cybersecurity Frameworks and Standards
Cybersecurity frameworks are guidelines that help organisations to secure their assets(digital and hardware) and manage risks, there are various cybersecurity frameworks used, some of them are:
- NIST Cybersecurity Framework: A widely used model that organizes cybersecurity activities into key functions:
- Govern
- Identify
- Protect
- Detect
- Respond
- Recover
- ISO/IEC 27001: An international standard for building an Information Security Management System (ISMS) focused on risk management and continuous improvement.
- Zero Trust Security Model: A modern approach based on the principle: “Never trust, always verify.” It requires continuous authentication, strict access control, and constant monitoring.
- CIS Controls: Prioritised, actionable best practices from the Center for Internet Security (CIS) to defend against common cyber attacks.
- SOC 2: For service providers, focuses on controls for security, availability, processing integrity, confidentiality, and privacy of customer data.
- HIPAA: For healthcare organisations, protects Protected Health Information (PHI).
Note: There are many other frameworks depending on the sectors they are used in.
Building a Practical Cybersecurity Program
- Know What You Have
Inventory devices, users, applications, and data. - Identify Critical Assets
Determine which systems and data are most valuable. - Reduce Common Risks
Enable multi-factor authentication, apply updates, and remove unused access. - Monitor and Detect Threats
Use logs, alerts, and endpoint protection tools. - Prepare for Incidents
Create an incident response plan and practice it. - Continuously Improve
Measure progress using frameworks and regular assessments.
Cybersecurity Best Practices for Individuals
- Use strong, unique passwords with a password manager
- Enable multi-factor authentication
- Keep devices and software updated
- Back up important data regularly
- Avoid suspicious links and downloads
- Secure home Wi-Fi networks
- Encrypt devices and lock screens
- Don’t share access and passwords with anyone
Cybersecurity Careers and Skills
There are various roles in cybersecurity, as we have covered cybersecurity is a vast field and offers various challenges, to get a role in cybersecurity you need to learn skill which can be done through obtaining certifications offered be companies like Cisco, Google, Juniper etc. You can visit their site and search for career path certifications. These are the roles that you can expect in cybersecurity:
- Security Analyst
- Penetration tester / Ethical Hacker
- GRC (Governance, Risk, & Compliance) Specialist
- Cloud security specialist
- Security Architect
- Digital Forensics Expert
FAQs
What is cybersecurity in simple words?
Cybersecurity is the practice of protecting digital systems and data from online threats.
What are the main types of cybersecurity?
Network security, application security, cloud security, endpoint security, IAM, and data security.
Is antivirus software enough?
No. Antivirus is helpful, but modern security requires multiple layers of protection.
What is the biggest cybersecurity threat today?
Stolen credentials and phishing attacks remain among the most common threats.
What is Zero Trust security?
A model that requires continuous verification of users and devices instead of assuming trust.


